- A lack of high-skill labor increases the cost of internal security, making outsourcing more appealing.
- It is unclear what processes could or should be outsourced versus what functions should remain in-house.
- It is not feasible to have 24/7/365 monitoring in-house for most firms.
Our Advice
Critical Insight
- You are outsourcing support, not accountability, unless you preface that with your customer.
- For most of you, you won’t have a choice – you’ll have to outsource high-end security skills to meet future needs.
- Third-party service providers may be able to more effectively remediate threats because of their large, disparate customer base and wider scope.
Impact and Result
- Documented obligations and processes. This will allow you to determine which solution (outsourcing vs. insourcing) allows for the best use of resources, and maintains your brand reputation.
- A list of variables and features to rank potential third-party providers vs. internal delivery to find which solution provides the best fit for your organization.
- Current limitations of your environment and the limitations of third parties identified for the environments you are looking to mature.
- Security responsibilities determined that can be outsourced, and which should be outsourced in order to gain resource allocation and effectiveness, and to improve your overall security posture.
- The limitations or restrictions for third-party usage understood.
Member Testimonials
After each Info-Tech experience, we ask our members to quantify the real-time savings, monetary impact, and project improvements our research helped them achieve. See our top member experiences for this blueprint and what our clients have to say.
Client
Experience
Impact
$ Saved
Days Saved
Town Of Halton Hills
Guided Implementation
8/10
N/A
N/A
_preview3848.jpg) Design and Implement a Business-Aligned Security Program
Design and Implement a Business-Aligned Security Program
_-_16x9_-_hires_previewb049.png) Build an Information Security Strategy
Build an Information Security Strategy
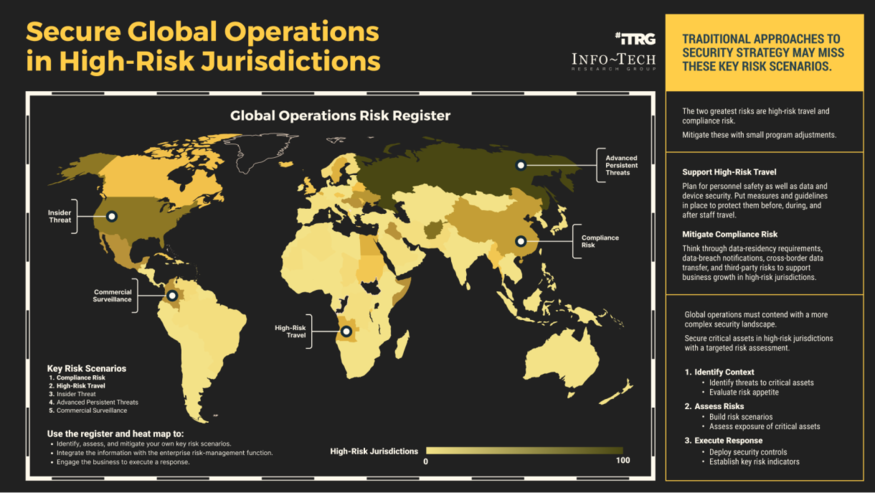 Secure Operations in High-Risk Jurisdictions
Secure Operations in High-Risk Jurisdictions
 Develop a Security Awareness and Training Program That Empowers End Users
Develop a Security Awareness and Training Program That Empowers End Users
 Build, Optimize, and Present a Risk-Based Security Budget
Build, Optimize, and Present a Risk-Based Security Budget
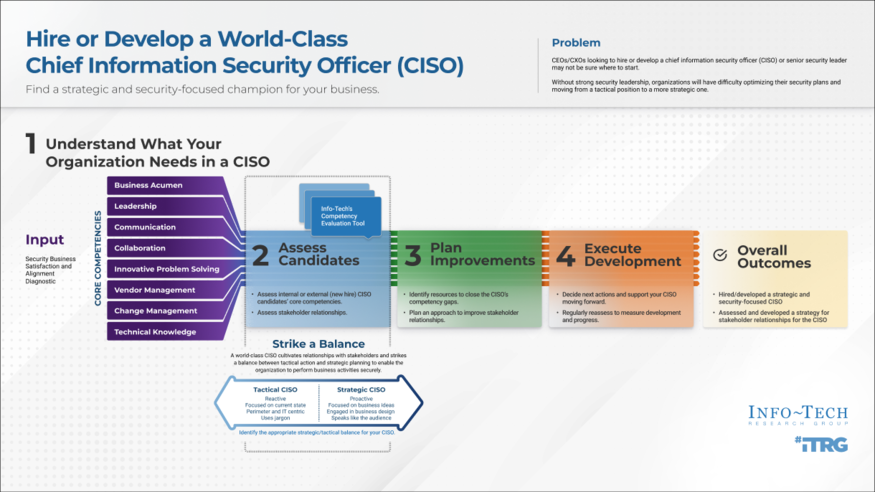 Hire or Develop a World-Class CISO
Hire or Develop a World-Class CISO
 Fast Track Your GDPR Compliance Efforts
Fast Track Your GDPR Compliance Efforts
 Build a Cloud Security Strategy
Build a Cloud Security Strategy
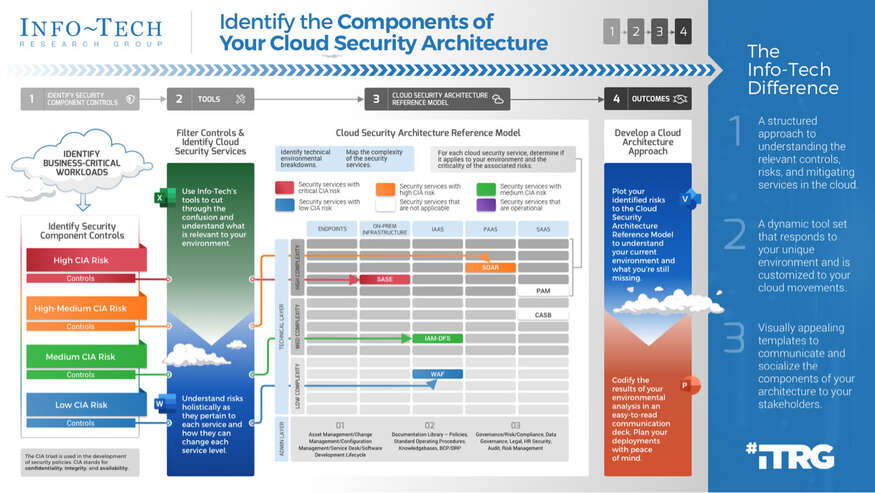 Identify the Components of Your Cloud Security Architecture
Identify the Components of Your Cloud Security Architecture
 Security Priorities 2022
Security Priorities 2022
 2020 Security Priorities Report
2020 Security Priorities Report
 Manage Third-Party Service Security Outsourcing
Manage Third-Party Service Security Outsourcing
 Select a Security Outsourcing Partner
Select a Security Outsourcing Partner
 Improve Security Governance With a Security Steering Committee
Improve Security Governance With a Security Steering Committee
 The First 100 Days as CISO
The First 100 Days as CISO
 Determine Your Zero Trust Readiness
Determine Your Zero Trust Readiness
 Cost-Optimize Your Security Budget
Cost-Optimize Your Security Budget
 Threat Preparedness Using MITRE ATT&CK®
Threat Preparedness Using MITRE ATT&CK®
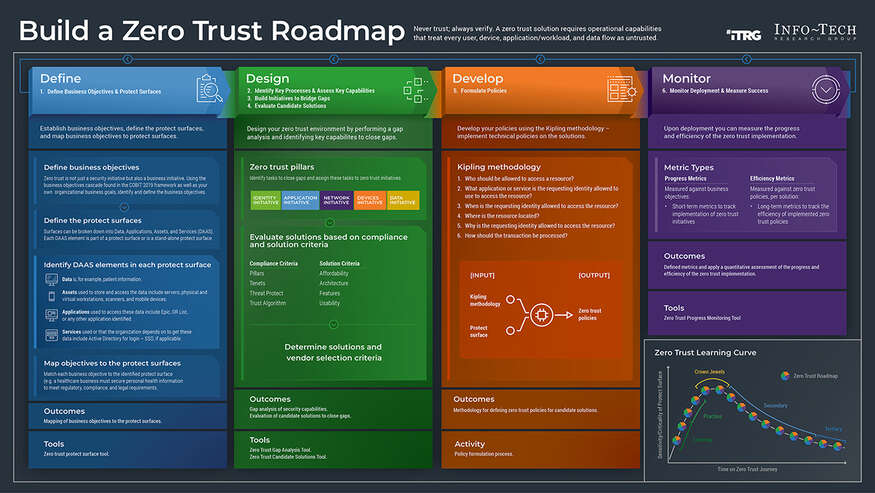 Build a Zero Trust Roadmap
Build a Zero Trust Roadmap
 Security Priorities 2023
Security Priorities 2023
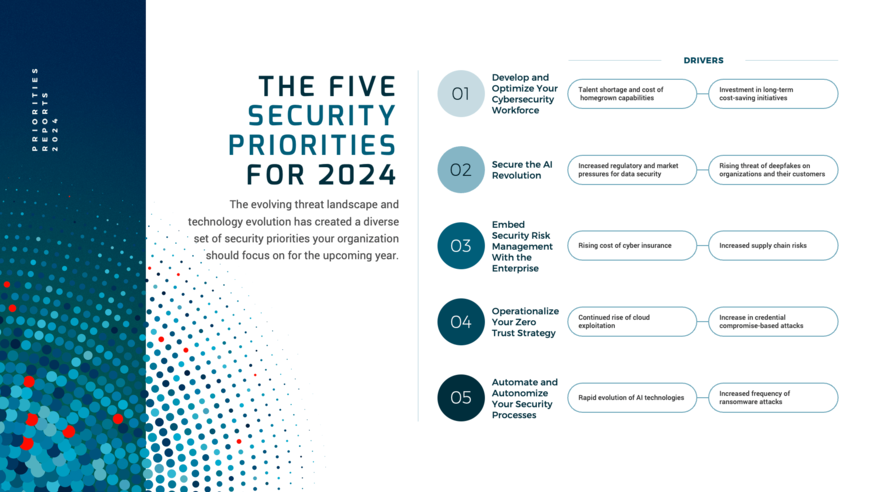 Security Priorities 2024
Security Priorities 2024
 Grow Your Own Cybersecurity Team
Grow Your Own Cybersecurity Team
 Security Priorities 2025
Security Priorities 2025
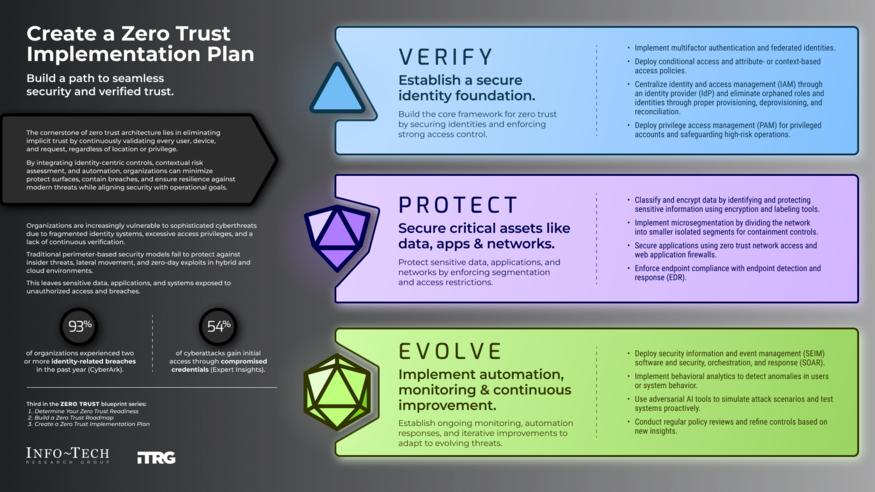 Create a Zero Trust Implementation Plan
Create a Zero Trust Implementation Plan
 Build Adaptive Security Services
Build Adaptive Security Services