- Year after year, CISOs need to develop a comprehensive security budget that is able to mitigate against threats.
- This budget will have to be defended against many other stakeholders to ensure there is proper funding.
- Security budgets are unlike other departmental budgets. Increases or decreases in the budget can drastically affect the organizational risk level.
- CISOs struggle with the ability to assess the effectiveness of their security controls and where to allocate money.
Our Advice
Critical Insight
- CISOs can demonstrate the value of security when they correlate mitigations to business operations and attribute future budgetary needs to business evolution.
- To identify the critical areas and issues that must be reflected in your security budget, develop a comprehensive corporate risk analysis and mitigation effectiveness model, which will illustrate where the moving targets are in your security posture.
Impact and Result
- Info-Tech’s methodology moves you away from the traditional budgeting approach to building a budget that is designed to be as dynamic as the business growth model.
- Collect your organization's requirements and build different budget options to describe how increases and decreases can affect the risk level.
- Discuss the different budgets with the business to determine what level of funding is needed for the desired level of security.
- Gain
approval of your budget early by preshopping and presenting the
budget to individual stakeholders prior to the final budget approval process.
_preview3848.jpg) Design and Implement a Business-Aligned Security Program
Design and Implement a Business-Aligned Security Program
_-_16x9_-_hires_previewb049.png) Build an Information Security Strategy
Build an Information Security Strategy
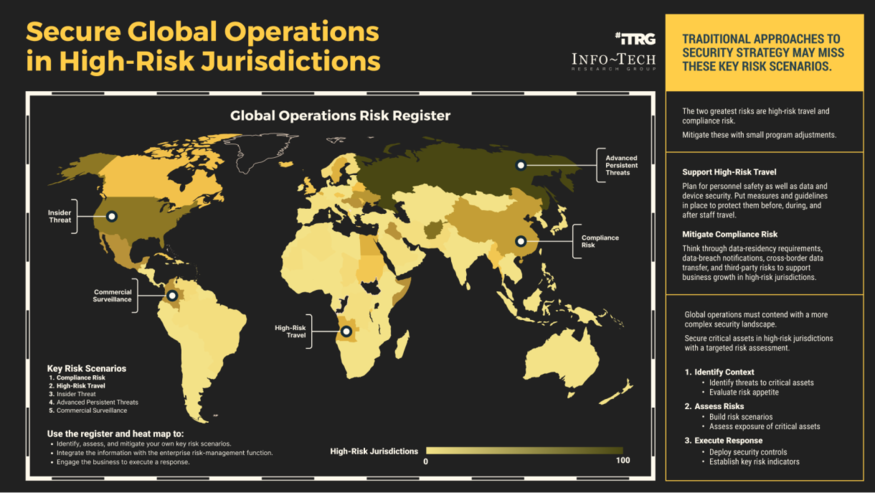 Secure Operations in High-Risk Jurisdictions
Secure Operations in High-Risk Jurisdictions
 Develop a Security Awareness and Training Program That Empowers End Users
Develop a Security Awareness and Training Program That Empowers End Users
 Build, Optimize, and Present a Risk-Based Security Budget
Build, Optimize, and Present a Risk-Based Security Budget
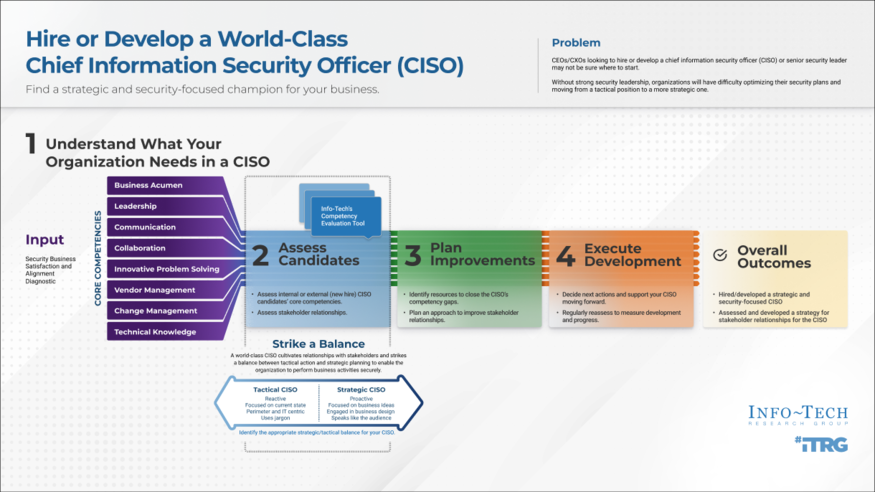 Hire or Develop a World-Class CISO
Hire or Develop a World-Class CISO
 Fast Track Your GDPR Compliance Efforts
Fast Track Your GDPR Compliance Efforts
 Build a Cloud Security Strategy
Build a Cloud Security Strategy
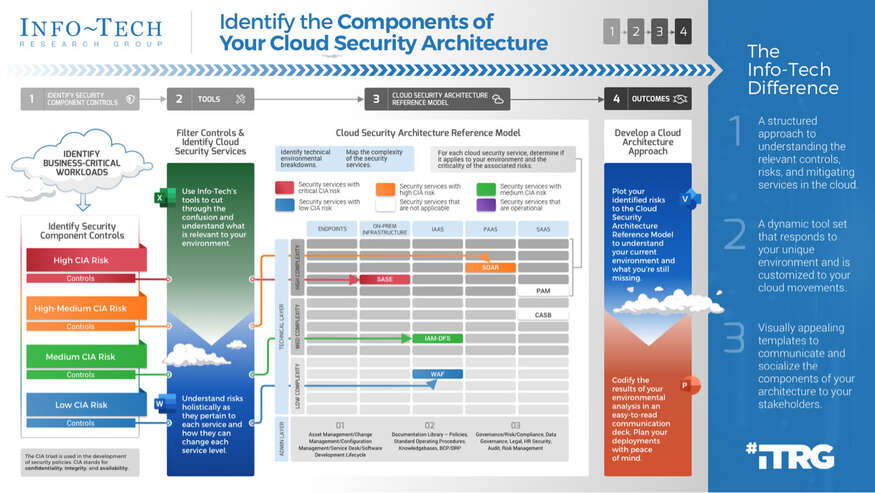 Identify the Components of Your Cloud Security Architecture
Identify the Components of Your Cloud Security Architecture
 Security Priorities 2022
Security Priorities 2022
 2020 Security Priorities Report
2020 Security Priorities Report
 Manage Third-Party Service Security Outsourcing
Manage Third-Party Service Security Outsourcing
 Select a Security Outsourcing Partner
Select a Security Outsourcing Partner
 Improve Security Governance With a Security Steering Committee
Improve Security Governance With a Security Steering Committee
 The First 100 Days as CISO
The First 100 Days as CISO
 Determine Your Zero Trust Readiness
Determine Your Zero Trust Readiness
 Cost-Optimize Your Security Budget
Cost-Optimize Your Security Budget
 Threat Preparedness Using MITRE ATT&CK®
Threat Preparedness Using MITRE ATT&CK®
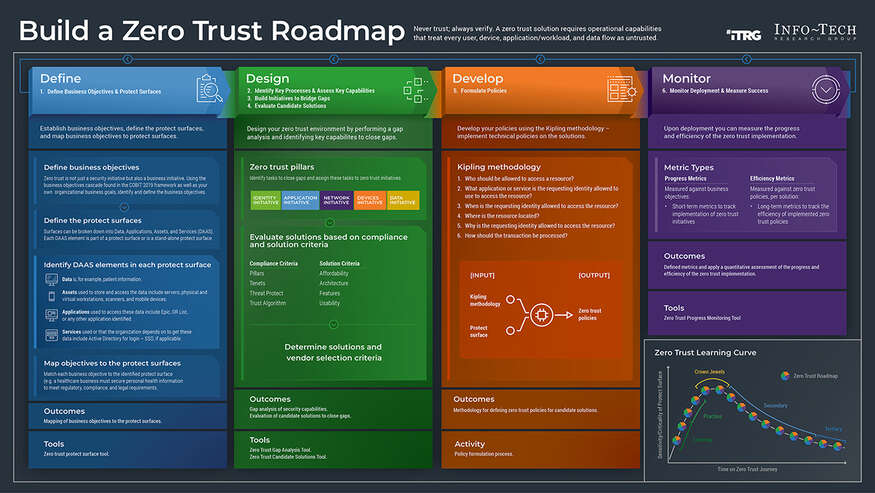 Build a Zero Trust Roadmap
Build a Zero Trust Roadmap
 Security Priorities 2023
Security Priorities 2023
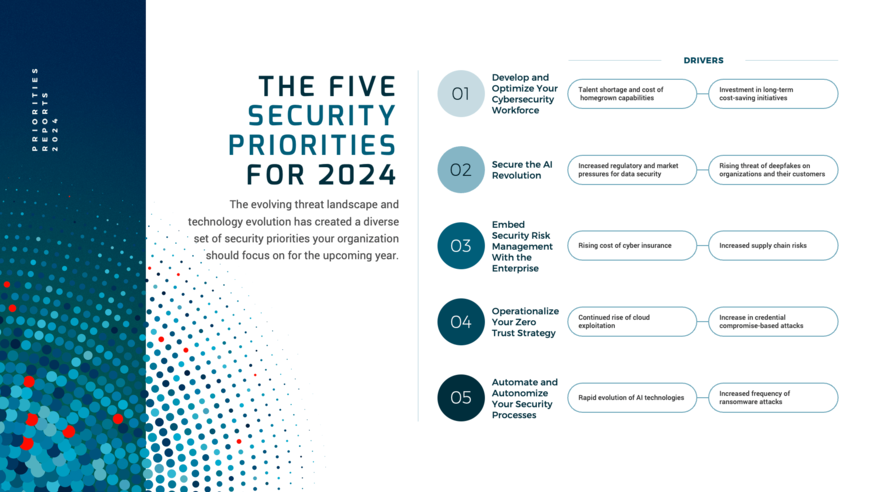 Security Priorities 2024
Security Priorities 2024
 Grow Your Own Cybersecurity Team
Grow Your Own Cybersecurity Team
 Security Priorities 2025
Security Priorities 2025
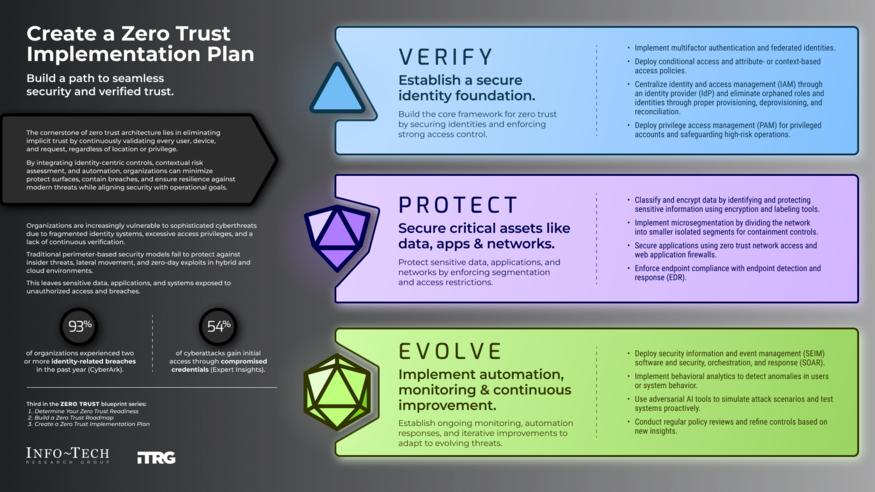 Create a Zero Trust Implementation Plan
Create a Zero Trust Implementation Plan
 Build Adaptive Security Services
Build Adaptive Security Services