- Leveraging the cloud introduces IT professionals to a new world that they are tasked with securing.
- With many cloud vendors proposing to share the security responsibility, it can be a challenge for organizations to develop a clear understanding of how they can best secure their data off premises.
Our Advice
Critical Insight
- Cloud security is not fundamentally different from security on premises.
- While some of the mechanics are different, the underlying principles are the same. Accountability doesn’t disappear.
- By virtue of its broad network accessibility, the cloud does expose decisions to extreme scrutiny, however.
Impact and Result
- The business is adopting a cloud environment and it must be secured, which includes:
- Ensuring business data cannot be leaked or stolen.
- Maintaining privacy of data and other information.
- Securing the network connection points.
- This blueprint and associated tools are scalable for all types of organizations within various industry sectors.
Member Testimonials
After each Info-Tech experience, we ask our members to quantify the real-time savings, monetary impact, and project improvements our research helped them achieve. See our top member experiences for this blueprint and what our clients have to say.
10.0/10
Overall Impact
$50,000
Average $ Saved
20
Average Days Saved
Client
Experience
Impact
$ Saved
Days Saved
Canadian Wildlife Federation
Guided Implementation
10/10
$50,000
20
Petar provided excellent guidance to help our security team learn best practices through discussion, establish a baseline for organizational report... Read More
_preview3848.jpg) Design and Implement a Business-Aligned Security Program
Design and Implement a Business-Aligned Security Program
_-_16x9_-_hires_previewb049.png) Build an Information Security Strategy
Build an Information Security Strategy
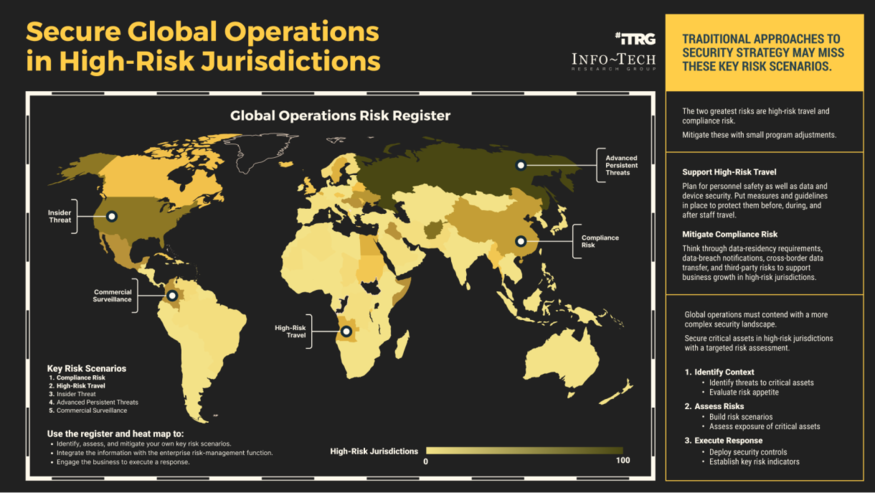 Secure Operations in High-Risk Jurisdictions
Secure Operations in High-Risk Jurisdictions
 Develop a Security Awareness and Training Program That Empowers End Users
Develop a Security Awareness and Training Program That Empowers End Users
 Build, Optimize, and Present a Risk-Based Security Budget
Build, Optimize, and Present a Risk-Based Security Budget
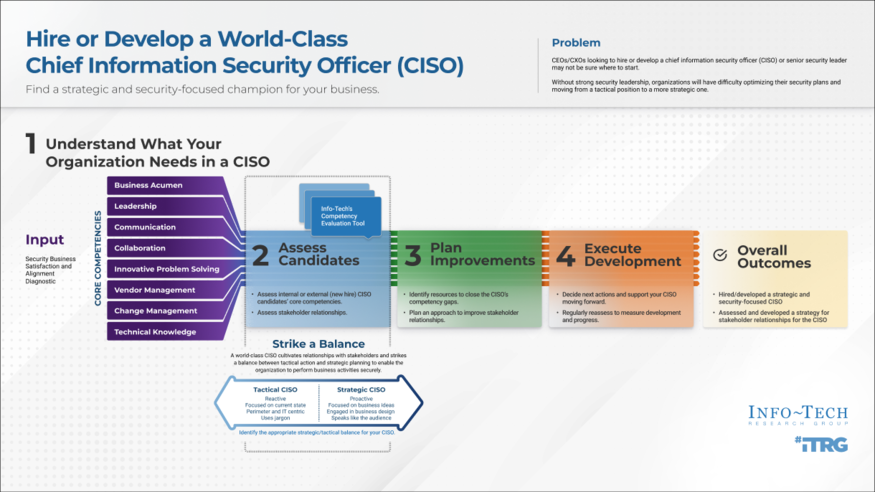 Hire or Develop a World-Class CISO
Hire or Develop a World-Class CISO
 Fast Track Your GDPR Compliance Efforts
Fast Track Your GDPR Compliance Efforts
 Build a Cloud Security Strategy
Build a Cloud Security Strategy
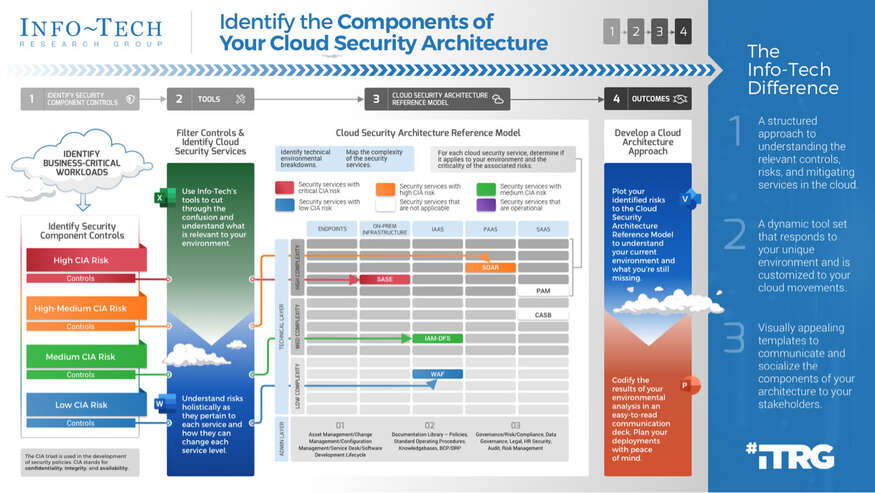 Identify the Components of Your Cloud Security Architecture
Identify the Components of Your Cloud Security Architecture
 Security Priorities 2022
Security Priorities 2022
 2020 Security Priorities Report
2020 Security Priorities Report
 Manage Third-Party Service Security Outsourcing
Manage Third-Party Service Security Outsourcing
 Select a Security Outsourcing Partner
Select a Security Outsourcing Partner
 Improve Security Governance With a Security Steering Committee
Improve Security Governance With a Security Steering Committee
 The First 100 Days as CISO
The First 100 Days as CISO
 Determine Your Zero Trust Readiness
Determine Your Zero Trust Readiness
 Cost-Optimize Your Security Budget
Cost-Optimize Your Security Budget
 Threat Preparedness Using MITRE ATT&CK®
Threat Preparedness Using MITRE ATT&CK®
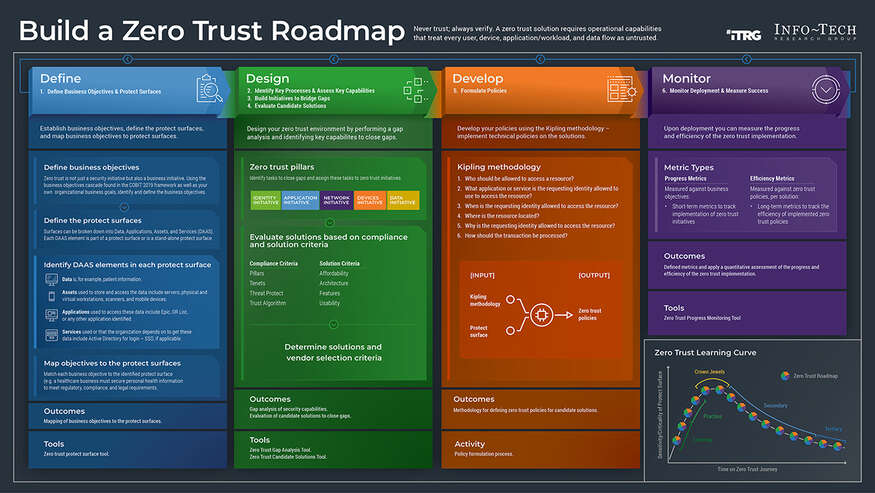 Build a Zero Trust Roadmap
Build a Zero Trust Roadmap
 Security Priorities 2023
Security Priorities 2023
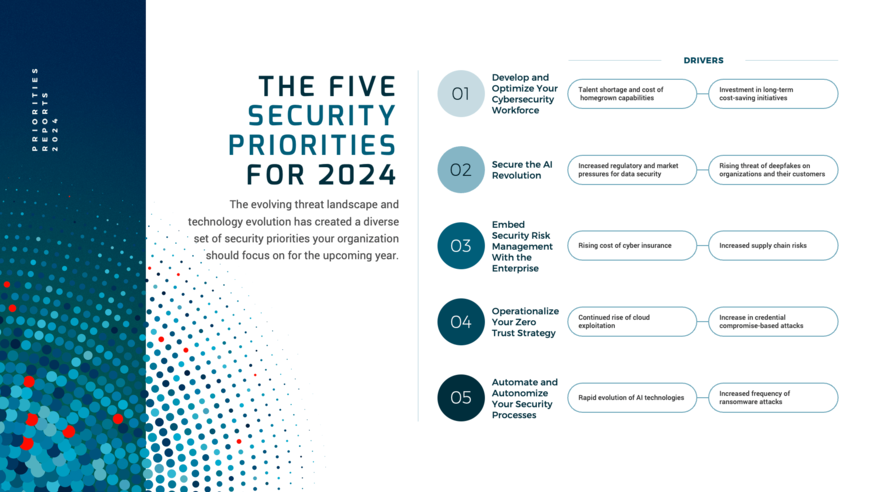 Security Priorities 2024
Security Priorities 2024
 Grow Your Own Cybersecurity Team
Grow Your Own Cybersecurity Team
 Security Priorities 2025
Security Priorities 2025
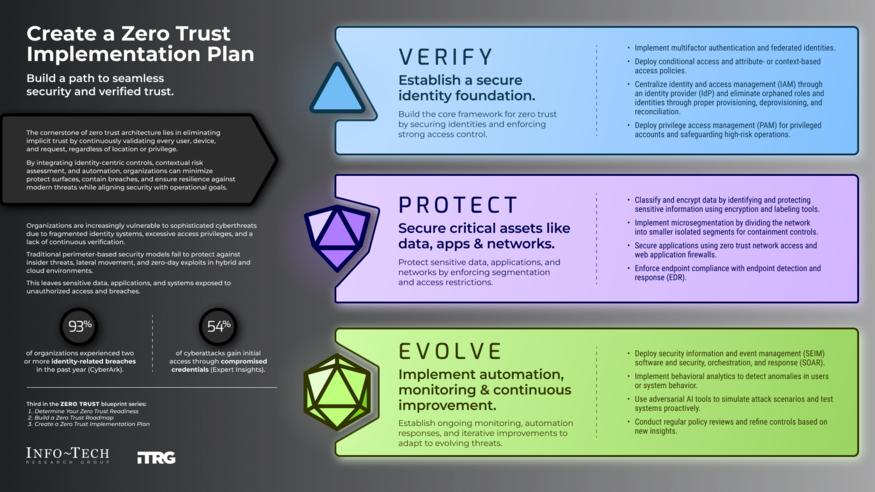 Create a Zero Trust Implementation Plan
Create a Zero Trust Implementation Plan
 Build Adaptive Security Services
Build Adaptive Security Services