- The fast evolution of the cybersecurity landscape requires security training and awareness programs that are frequently updated and improved.
- Security and awareness training programs often fail to engage end users. Lack of engagement can lead to low levels of knowledge retention.
- Irrelevant or outdated training content does not properly prepare your end users to effectively defend the organization against security threats.
Our Advice
Critical Insight
- One-time, annual training is no longer sufficient for creating an effective security awareness and training program.
- By presenting security as a personal and individualized issue, you can make this new personal focus a driver for your organizational security awareness and training program.
Impact and Result
- Create a training program that delivers smaller amounts of information on a more frequent basis to minimize effort, reduce end-user training fatigue, and improve content relevance.
- Evaluate and improve your security awareness and training program continuously to keep its content up-to-date. Leverage end-user feedback to ensure content remains relevant to those who receive it.
Member Testimonials
After each Info-Tech experience, we ask our members to quantify the real-time savings, monetary impact, and project improvements our research helped them achieve. See our top member experiences for this blueprint and what our clients have to say.
9.0/10
Overall Impact
$7,399
Average $ Saved
5
Average Days Saved
Client
Experience
Impact
$ Saved
Days Saved
Enable Ireland
Guided Implementation
9/10
$7,399
5
Process was simple and Victor Okorie deeply knowledgeable and easy to deal with.
_preview3848.jpg) Design and Implement a Business-Aligned Security Program
Design and Implement a Business-Aligned Security Program
_-_16x9_-_hires_previewb049.png) Build an Information Security Strategy
Build an Information Security Strategy
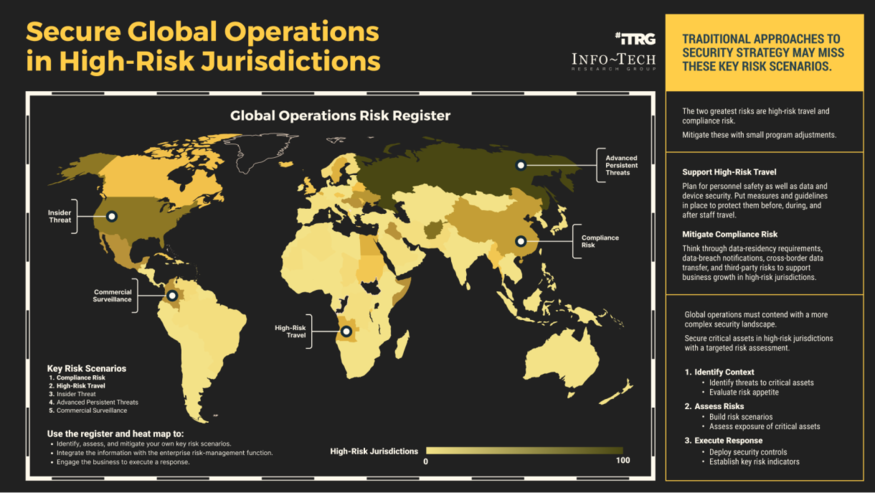 Secure Operations in High-Risk Jurisdictions
Secure Operations in High-Risk Jurisdictions
 Develop a Security Awareness and Training Program That Empowers End Users
Develop a Security Awareness and Training Program That Empowers End Users
 Build, Optimize, and Present a Risk-Based Security Budget
Build, Optimize, and Present a Risk-Based Security Budget
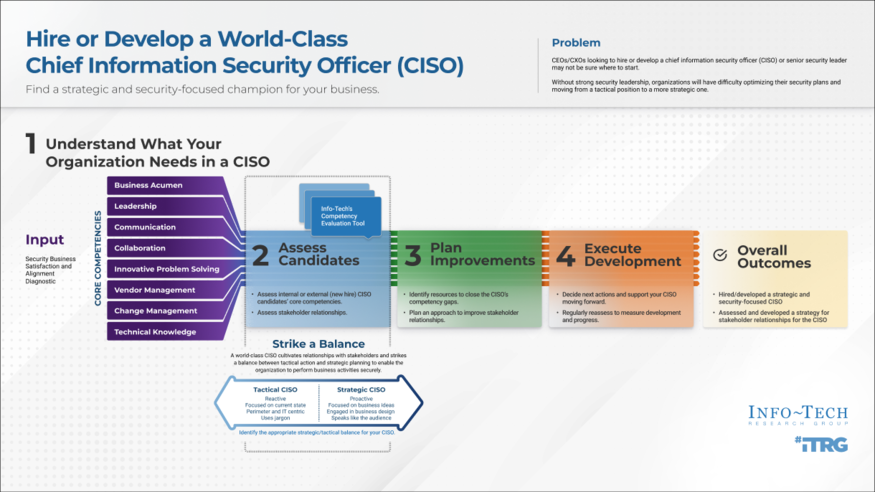 Hire or Develop a World-Class CISO
Hire or Develop a World-Class CISO
 Fast Track Your GDPR Compliance Efforts
Fast Track Your GDPR Compliance Efforts
 Build a Cloud Security Strategy
Build a Cloud Security Strategy
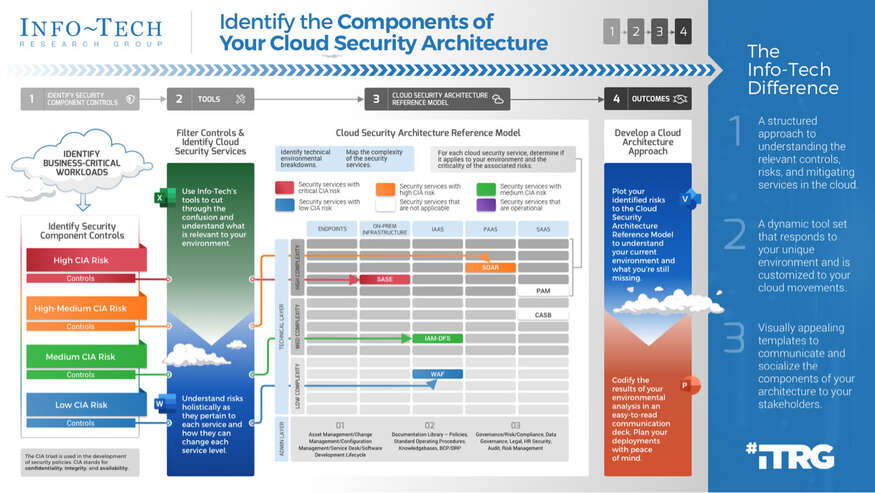 Identify the Components of Your Cloud Security Architecture
Identify the Components of Your Cloud Security Architecture
 Security Priorities 2022
Security Priorities 2022
 2020 Security Priorities Report
2020 Security Priorities Report
 Manage Third-Party Service Security Outsourcing
Manage Third-Party Service Security Outsourcing
 Select a Security Outsourcing Partner
Select a Security Outsourcing Partner
 Improve Security Governance With a Security Steering Committee
Improve Security Governance With a Security Steering Committee
 The First 100 Days as CISO
The First 100 Days as CISO
 Determine Your Zero Trust Readiness
Determine Your Zero Trust Readiness
 Cost-Optimize Your Security Budget
Cost-Optimize Your Security Budget
 Threat Preparedness Using MITRE ATT&CK®
Threat Preparedness Using MITRE ATT&CK®
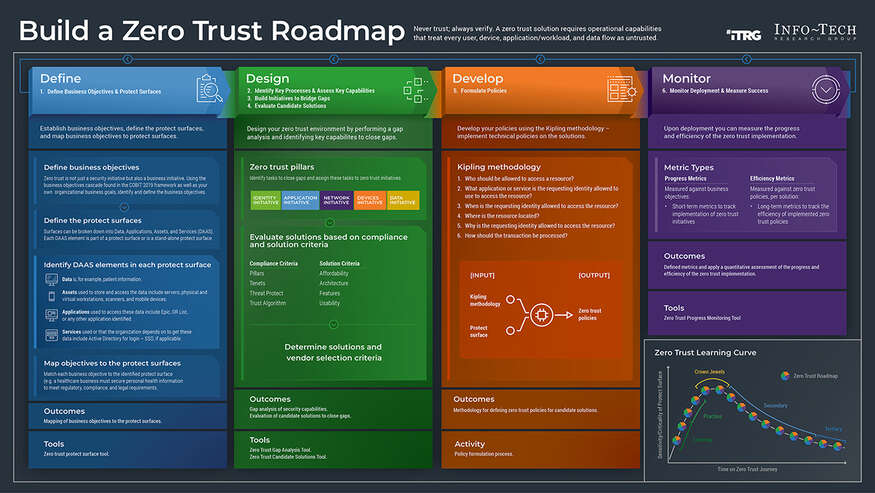 Build a Zero Trust Roadmap
Build a Zero Trust Roadmap
 Security Priorities 2023
Security Priorities 2023
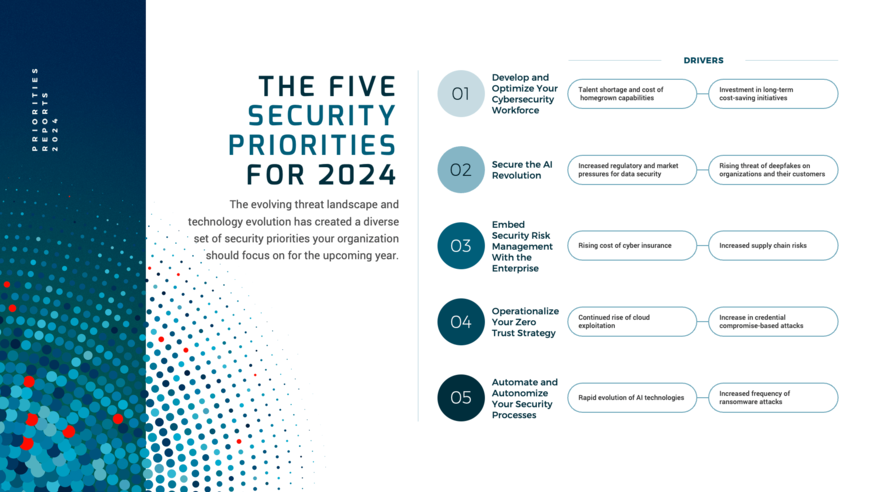 Security Priorities 2024
Security Priorities 2024
 Grow Your Own Cybersecurity Team
Grow Your Own Cybersecurity Team
 Security Priorities 2025
Security Priorities 2025
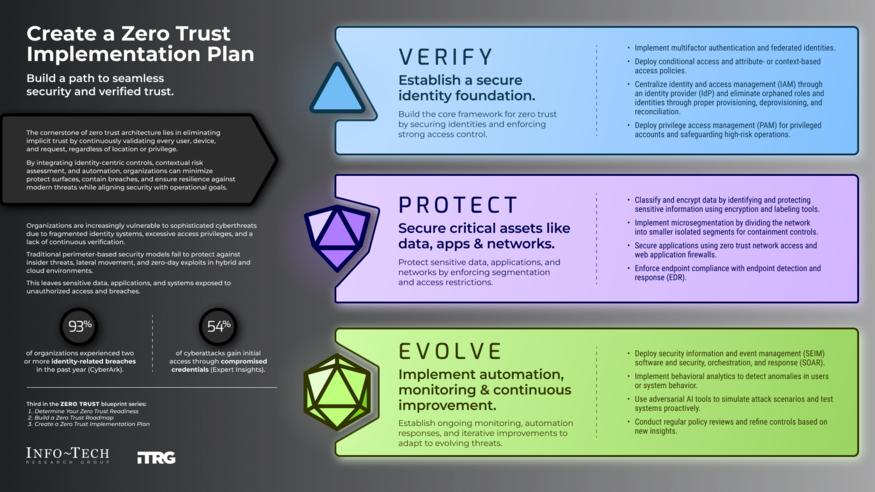 Create a Zero Trust Implementation Plan
Create a Zero Trust Implementation Plan
 Build Adaptive Security Services
Build Adaptive Security Services